The insider threat is one of the most dangerous and at the same time inherited topics in the field of cybercrime. About cases, when employees of organizations help hackers from the inside, Little is known, And the units are publicly resolved to talk about this. BBC journalist Joe Tidi (Joe Tidy) Read More …
Category: Blogs
Blog about things familiar to most people, from a non-standard point of view.
BlockBlasters: as a patch of popular game turned into a Trojan for theft of data and cryptocurrencies

Dangerous turn for your favorite game 31 July 2025 The years on Steam was a bright 2D platformer/Blockblasters shooter from the Genesis Interactive studio. In the first month, the game received hundreds of positive reviews and quickly won the attention of the audience thanks to dynamic gameplay. However 30 The developers released Augustus Read More …
How to hack and destroy nuclear power 49 minutes: Disassembly of cyber attacks for a nuclear reactor
Late September evening 2023 year. You lazily leaf through ebay. Among the usual junk comes across strange iron - heavy industrial modules. Siemens and Areva logos flaunts on boards. The description is scarce, But professional, The price is amazingly affordable. Here are the components of the TelePerm XS system - Read More …
Steam's alleged hacking is at risk 89 millions of accounts.
What happened? Reported, that data 89 Millions of Steam accounts were at risk due to the alleged leakage, associated with Twilio, service, which Steam uses to send SMS with 2FA codes. Flowing data, Including SMS logs, 2FA codes and metadata, Sold on dark Read More …
The distribution of malicious in Noodlophile under the guise of AI services video generation
Attackers began to use fake video generation tools using artificial intelligence, to spread a new type of malicious software - noodlophile, infostiler, disguised as the result of the work of "AI-services". Fraudulent sites use attractive names, such as Dream Machine, and are actively advertised through large Read More …
ATOMIC Stealer disguise for a hacked version of Evernote: Analysis MacOS attacks
Research Center Ahnlab Security Intelligence Center (Asec) revealed the distribution of the malicious program Atomic Stealer, disguised as the hacking version of Evernote. Atomic Stealer is an information, aimed at MacOS. He steals information from browsers, Key ligaments, cryptocurrencs and system data. Usually it spreads Read More …
Analysis of web browsers telemetry 2025
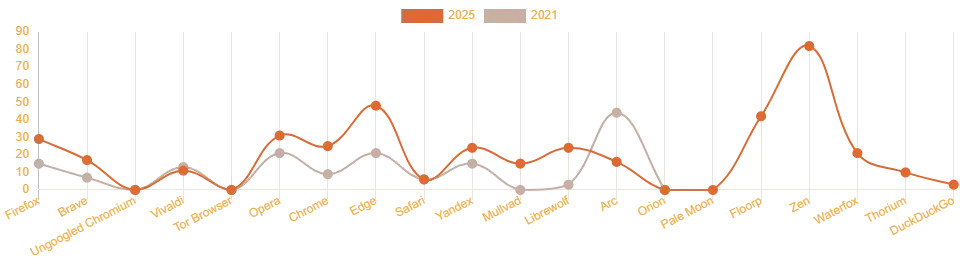
After the publication of the translation of the original article, prepared by the user SIZEOF, Colleagues asked to additionally test several browsers. The purpose of testing was to determine, What outgoing compounds are created after the installation of browsers and at their first launch. Refusal of liability data are provided as it is - without conclusions Read More …
cURL 27 years. The history of the creation and its author.
Today is performed 27 years since the creation of Curl – This is a command line based on the Libcurl library for transmitting data from the server and to the server using various protocols, Including http, https, FTP, FTPS, IMAP, IMAPS, Pop3, POP3S, Read More …
Secrets in “damaged” Winamp skins

A few years ago I collected materials for the Winamp Skin Museum, and some of the files seemed damaged to me. I decided to explore them, and it turned out, that in fact these skins are just zip files with a different extension. What will happen, if you extract these files? Read More …
The Rise and Fall of Yahoo! Messenger
Yahoo! Messenger was one of the first text messaging apps on the Internet. He made a real revolution in communication, offering users a convenient alternative to telephone conversations and email correspondence. Let's talk, how it appeared and why it could not compete with Read More …